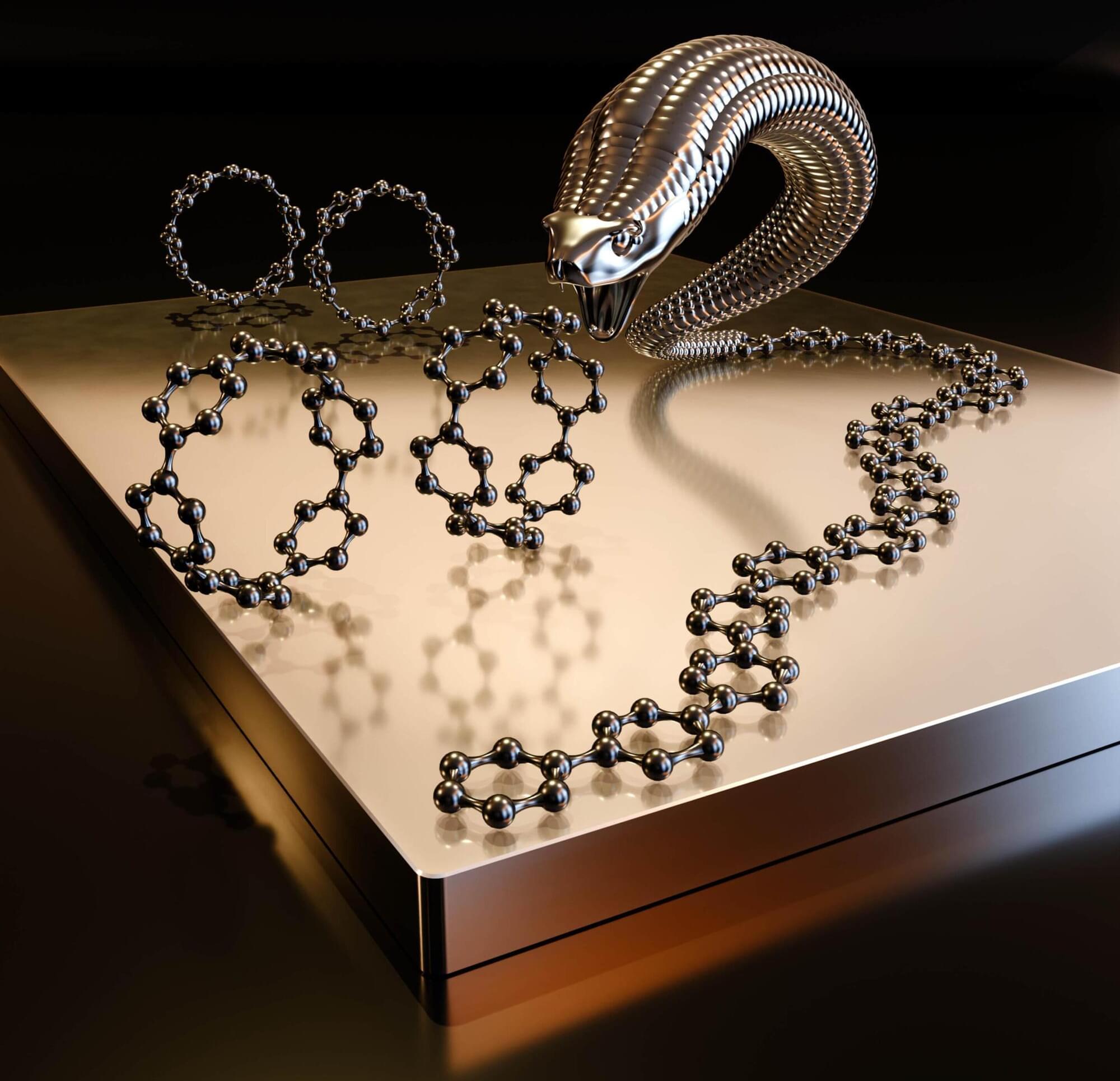
The longest chains of the conductive polymer poly(p-phenylene; PPP) produced to date are just under one micrometer (thousandth of a millimeter) long—almost an order of magnitude longer than previously possible. A research team from the fields of chemistry and physics led by Prof. Dr. Michael Gottfried from Marburg University, Germany, has demonstrated for the first time that PPP can be synthesized on surfaces via a specific ring-opening polymerization as genuine chain growth.
The statistically most frequently measured length is around 170 nanometers—with one outlier reaching nearly 1,000 nanometers—a record. The new, halogen-free process does not produce any disruptive by-products, thus opening up a particularly clean approach to ultra-long, conjugated polymer chains.
The results have been published by the interdisciplinary team from the Universities of Marburg, Giessen and Leipzig and Chinese researchers in the journal Nature Chemistry.