Quantum computers, systems that process information leveraging quantum mechanical effects, have the potential of outperforming classical computers on some tasks. Despite their potential, the use of these systems remains very limited, due to their high cost and other challenges that have so far prevented their large-scale fabrication.
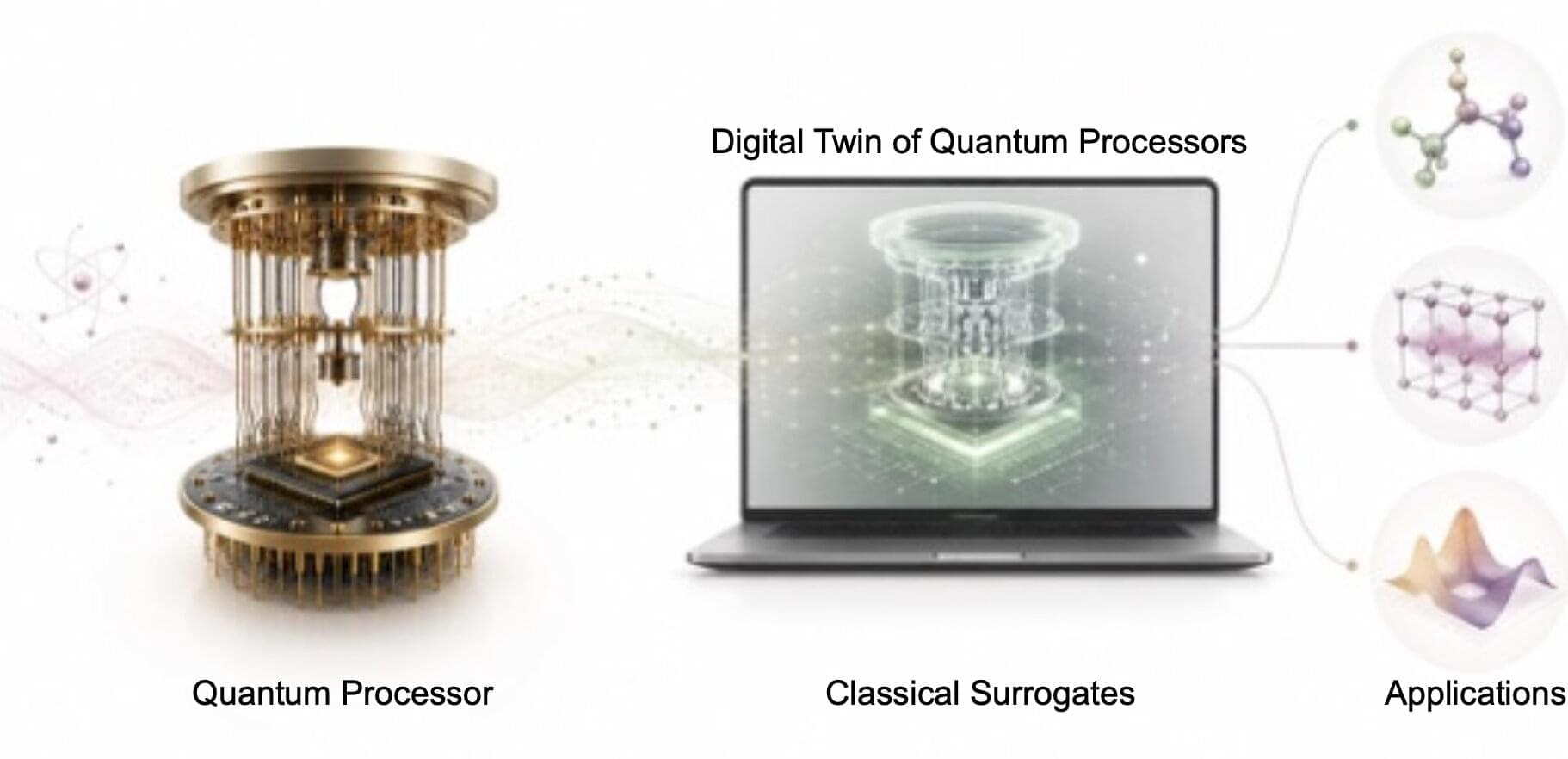
Researchers at the Henan Key Laboratory of Quantum Information and Cryptography and Nanyang Technological University have developed predictive surrogates, new computational models that can learn and reproduce the outputs of quantum processors.
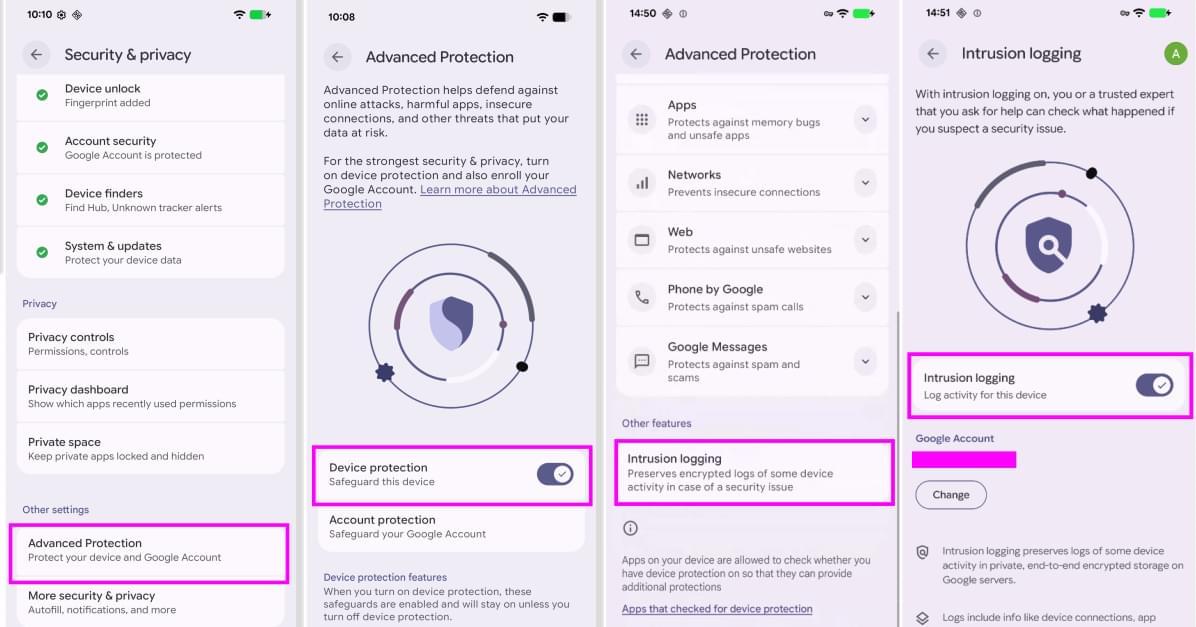
These models, introduced in a paper published in Nature Communications, could be used to extract useful information from quantum computers and perform computations more efficiently with provable guarantees, even if users do not have direct access to advanced and expensive quantum computing hardware.