The 2 SOPS or 2nd Space Operations Squadron commander, Lt Col Robert Wray… More.
Of all the missions the Space Force performs daily for a grateful nation, there is none more ubiquitous and essential than GPS. Today’s soldiers and sailors depend on reliable, accurate, and secure GPS as much as they do any weapon they employ. Meanwhile, the rest of the world is just as dependent on GPS to enable basic mobility and underpins every other sector of the modern global economy. The criticality of secure global navigation and timing to both warfighting and the national economy makes it unique – we simply could not go a day without space. In so few words, GPS’ future is ground zero for the new space race.
The 2 SOPS or 2nd Space Operations Squadron commander, Lt Col Robert Wray reminds me that “14 of the 16 critical infrastructures designated by the Department of Homeland Security rely on 24/7 GPS to operate for the country.” But the newest GPS satellites in use today are the same school bus sized ones Gen. Hyten has lamented are, “juicy targets” for our adversaries – marvels of modern engineering, yes, but no longer sufficient to meet modern needs.
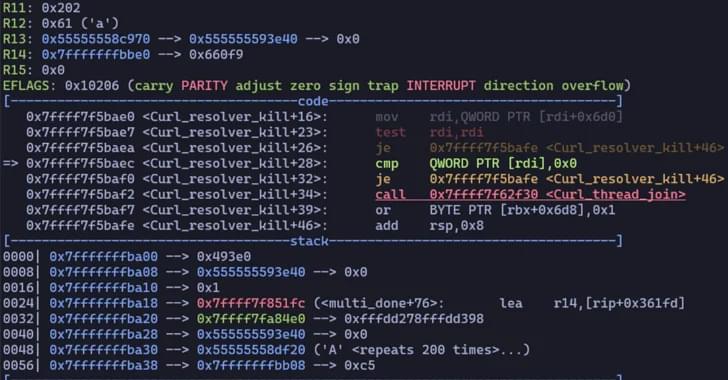
Alternatives to GPS, categorically called Global Navigation Satellite Systems (GNSS), are growing rapidly because the old GPS system we rely on offers neither the precision nor security needed in an increasingly autonomous, rule based, and precisely timed world. What exactly needs to change then, aside from smaller, faster satellites as technology becomes more efficient and readily available? There are major challenges with the current system that today’s Guardians are already working on. But to usher in a new and improved GPS capability, the government needs to adopt artificial intelligence and machine learning to enhance squadron operations, work to better integrate commercial software into current GPS constellation to get the most out of current capabilities, and continue to invest in the next generation of leaders. Private capital has begun aligning with companies aiming to solve these future deficiencies, in a race against pacing threats like China and Russia.