Google fixed 120 Android flaws in Sept 2025, including 2 exploited zero-days, reducing targeted attack risk.


MITs State of AI in Business report revealed that while 40% of organizations have purchased enterprise LLM subscriptions, over 90% of employees are actively using AI tools in their daily work. Similarly, research from Harmonic Security found that 45.4% of sensitive AI interactions are coming from personal email accounts, where employees are bypassing corporate controls entirely.
This has, understandably, led to plenty of concerns around a growing “Shadow AI Economy”. But what does that mean and how can security and AI governance teams overcome these challenges?

An international research team from the Max Planck Institute (MPI) for Informatics in Saarbrücken, Germany, and the Delft University of Technology in the Netherlands has developed a method to detect compromised hosts at an internet scale by probing servers with public SSH keys previously observed in attacker operations.
This way, the team was able to identify more than 16,000 compromised hosts. Their findings have now been published at the USENIX Security Symposium 2025, where they were awarded a Distinguished Paper Award and the Internet Defense Prize.
Secure Shell (SSH) is one of the most common tools used to manage servers remotely. It provides a secure, encrypted channel between a client and a server, allowing users to log in, execute commands, and transfer files safely. SSH is widely used by system administrators and developers for maintaining and configuring remote systems.



Microsoft has released the KB5064081 preview cumulative update for Windows 11 24H2, which includes thirty-six new features or changes, with many gradually rolling out. These updates include new Recall features and a new way of displaying CPU usage in Task Manager.
The KB5064081 update is part of the company’s optional non-security preview update schedule, which releases updates at the end of each month to test new fixes and features coming to the next month’s Patch Tuesday.
Unlike regular Patch Tuesday cumulative updates, monthly non-security preview updates do not include security updates and are optional.

WhatsApp has patched a security vulnerability in its iOS and macOS messaging clients that was exploited in targeted zero-day attacks.
The company says this zero-click flaw (tracked as CVE-2025–55177) affects WhatsApp for iOS prior to version 2.25.21.73, WhatsApp Business for iOS v2.25.21.78, and WhatsApp for Mac v2.25.21.78.
“Incomplete authorization of linked device synchronization messages in WhatsApp […] could have allowed an unrelated user to trigger processing of content from an arbitrary URL on a target’s device,” WhatsApp said in a Friday security advisory.

Microsoft has found no link between the August 2025 KB5063878 security update and customer reports of failure and data corruption issues affecting solid-state drives (SSDs) and hard disk drives (HDDs).
Redmond first told BleepingComputer last week that it is aware of users reporting SSD failures after installing this month’s Windows 11 24H2 security update.
In a subsequent service alert seen by BleepingComputer, Redmond said that it was unable to reproduce the issue on up-to-date systems and began collecting user reports with additional details from those affected.

Google now reports that the Salesloft Drift breach is larger than initially thought, warning that attackers also used stolen OAuth tokens to access a small number of Google Workspace email accounts in addition to stealing data from Salesforce instances.
Based on new information identified by GTIG, the scope of this compromise is not exclusive to the Salesforce integration with Salesloft Drift and impacts other integrations,’ warns Google.
We now advise all Salesloft Drift customers to treat any and all authentication tokens stored in or connected to the Drift platform as potentially compromised.
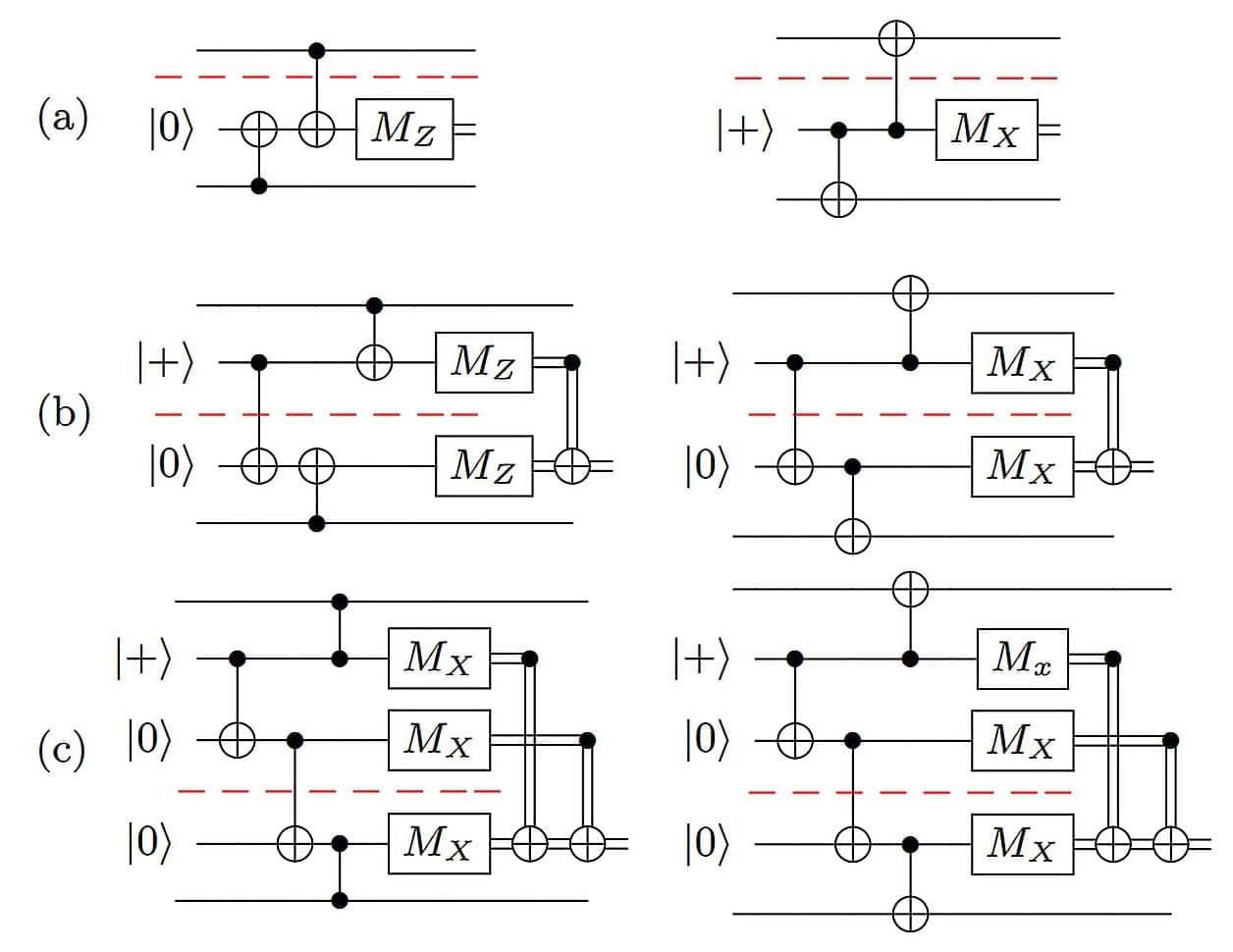
While quantum computers are already being used for research in chemistry, material science, and data security, most are still too small to be useful for large-scale applications. A study led by researchers at the University of California, Riverside, now shows how “scalable” quantum architectures—systems made up of many small chips working together as one powerful unit—can be made.