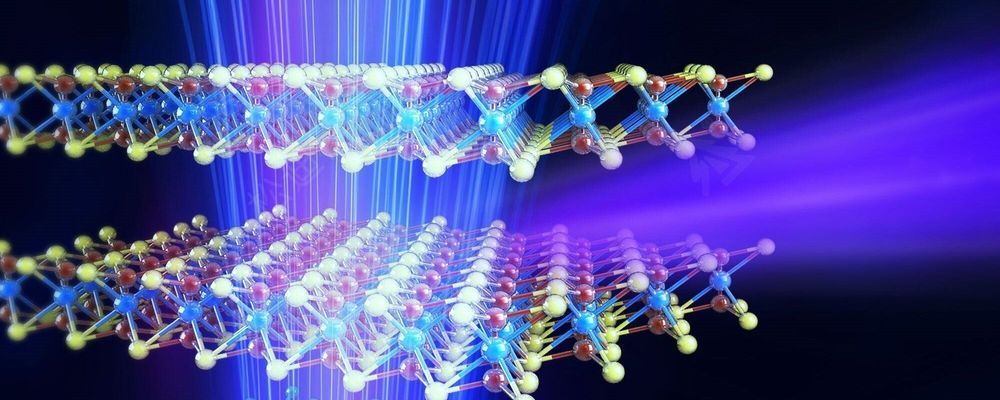
Technion researchers have developed accurate radiation sources that are expected to lead to breakthroughs in medical imaging and other areas. They have developed precise radiation sources that may replace the expensive and cumbersome facilities currently used for such tasks. The suggested apparatus produces controlled radiation with a narrow spectrum that can be tuned with high resolution, at a relatively low energy investment. The findings are likely to lead to breakthroughs in a variety of fields, including the analysis of chemicals and biological materials, medical imaging, X-ray equipment for security screening, and other uses of accurate X-ray sources.
Published in the journal Nature Photonics, the study was led by Professor Ido Kaminer and his master’s student Michael Shentcis as part of a collaboration with several research institutes at the Technion: the Andrew and Erna Viterbi Faculty of Electrical Engineering, the Solid State Institute, the Russell Berrie Nanotechnology Institute (RBNI), and the Helen Diller Center for Quantum Science, Matter and Engineering.
The researchers’ paper shows an experimental observation that provides the first proof-of-concept for theoretical models developed over the last decade in a series of constitutive articles. The first article on the subject also appeared in Nature Photonics. Written by Prof. Kaminer during his postdoc at MIT, under the supervision of Prof. Marin Soljacic and Prof. John Joannopoulos, that paper presented theoretically how two-dimensional materials can create X-rays. According to Prof. Kaminer, “that article marked the beginning of a journey towards radiation sources based on the unique physics of two-dimensional materials and their various combinations—heterostructures. We have built on the theoretical breakthrough from that article to develop a series of follow-up articles, and now, we are excited to announce the first experimental observation on the creation of X-ray radiation from such materials, while precisely controlling the radiation parameters.”