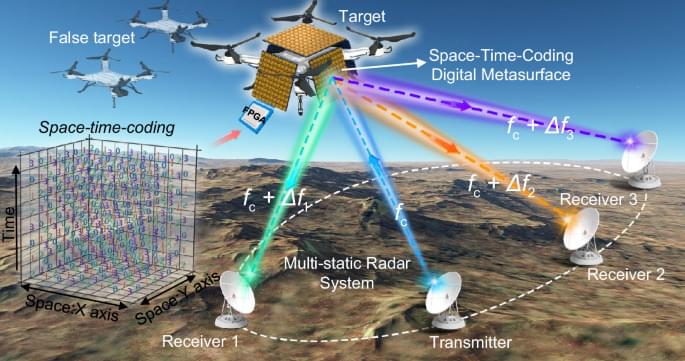
In advanced multi-static radar (MSR), multidimensional information from target echo signals is collected by different receivers to enable precise localization using various algorithms. Owing to its efficient target localization and tracking capability, MSR has found wide applications in sensing, military operations, aviation, and aerospace. Multi-static nature of MSR also makes it difficult to counter. Here, we propose an anti-radar methodology based on space-time-coding metasurface (STCM) to counter MSR. By designing the physical characteristics of STCM and developing adaptive and robust electronic countermeasure (ECM) control strategies, we realize a cost-effective, miniaturized and low-complexity ECM system with the flexible controlling capabilities. Under non-cooperative and dynamic ECM scenarios, the proposed method shows exceptional concealment and deception performance. To validate the methodology, we develop a prototype of the STCM-based anti-MSR system and successfully demonstrate its ability to neutralize various MSR technologies. The proposed method is expected to find practical applications in the anti-MSR scenarios.
This study proposes an anti-radar methodology based on space-time-coding metasurface to counter multi-static radar, which enables a cost-effective, miniaturized, and low complexity electronic countermeasure system.