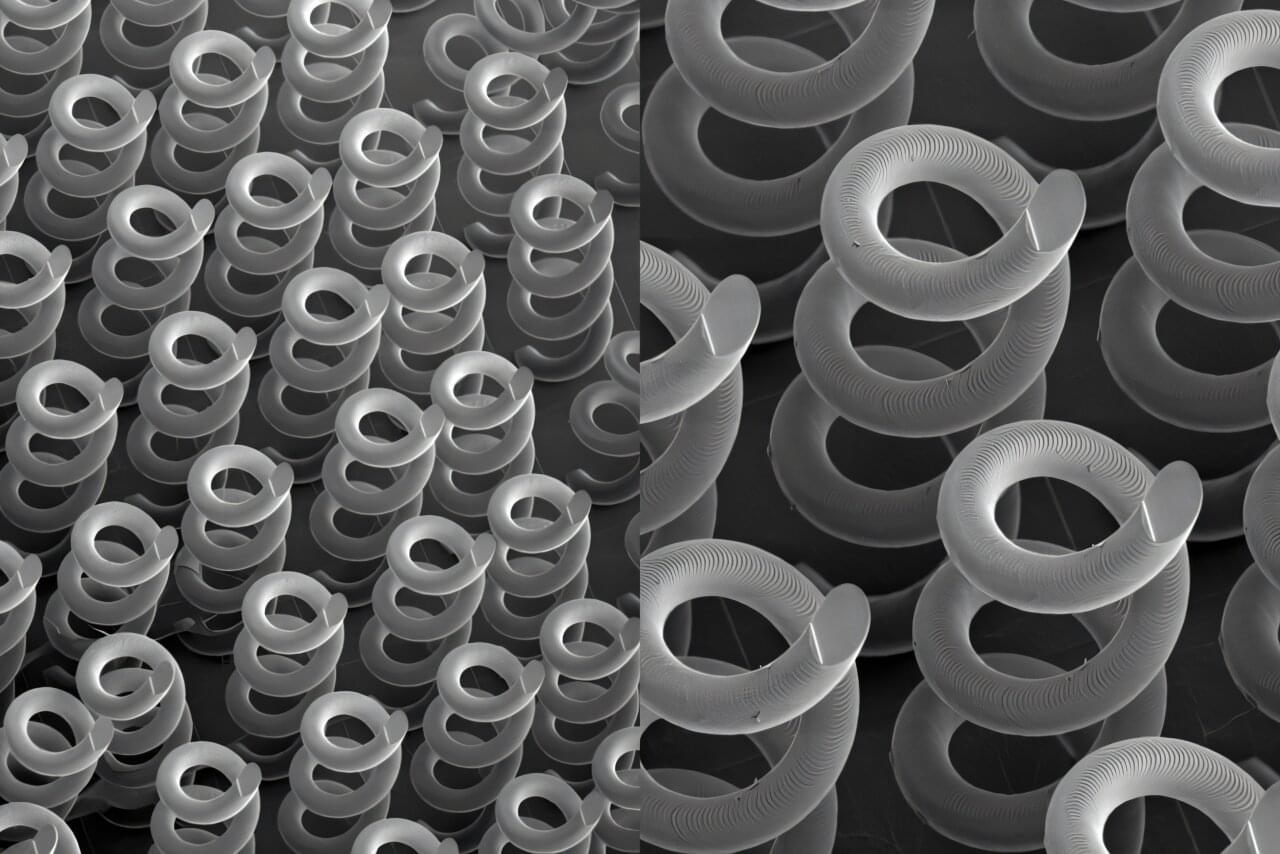
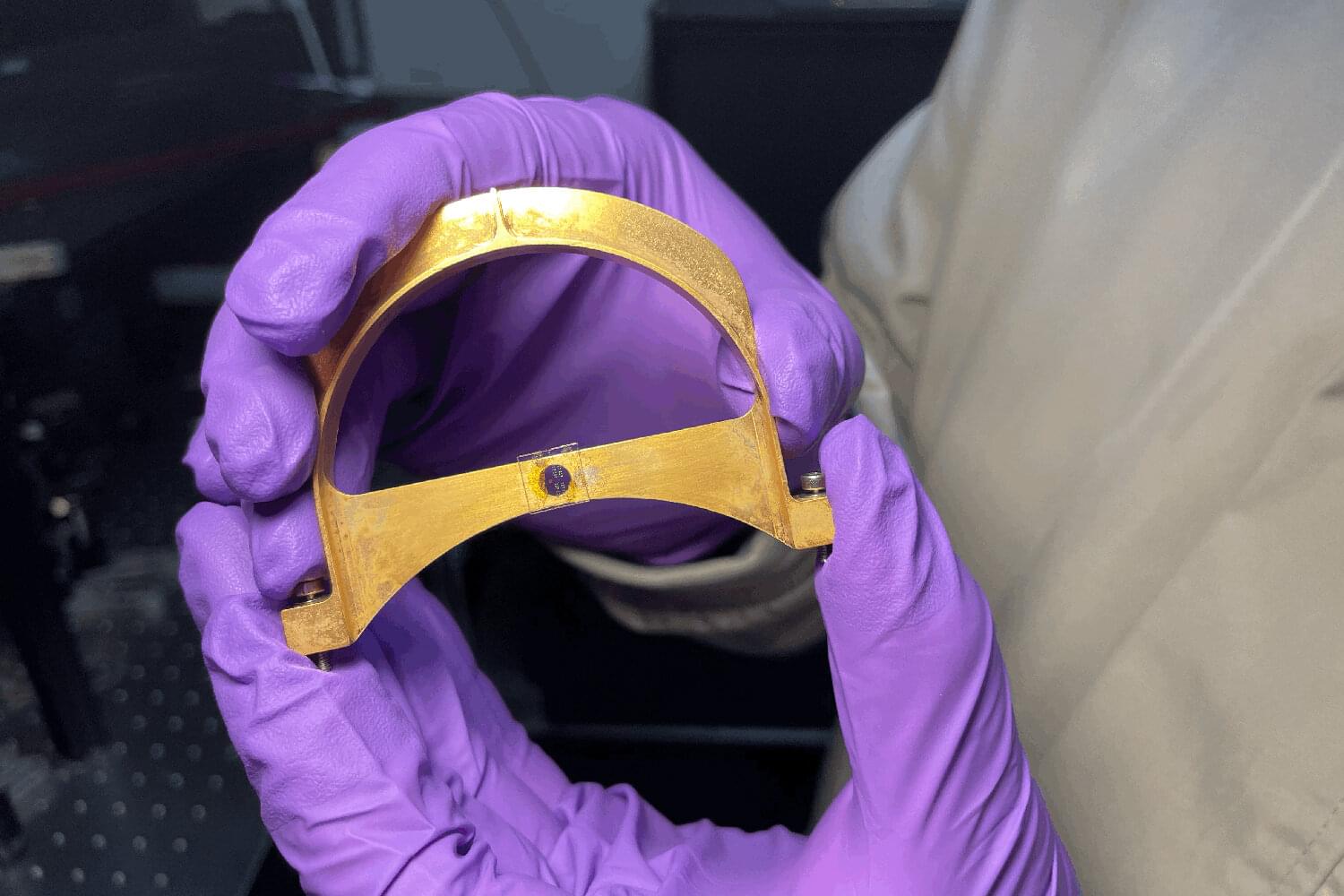
Microsoft is rolling out hardware-accelerated BitLocker in Windows 11 to address growing performance and security concerns by leveraging the capabilities of system-on-a-chip and CPU.
BitLocker is the native full-disk encryption feature in Windows that protects data from being readable without proper authentication. During normal device boot, it relies on the Trusted Platform Module (TPM) to securely manage encryption keys and automatically unlock the drive.
Microsoft states that as non-volatile memory express (NVMe) storage has become more performant, BitLocker’s cryptographic operations have a more noticeable performance impact for gaming and video editing activities.