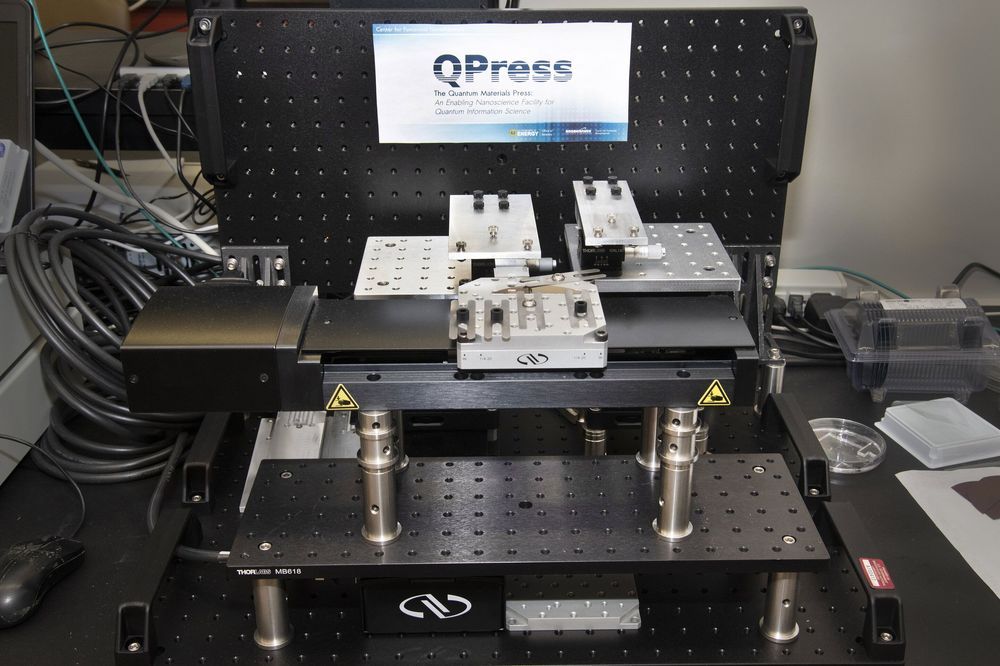
Checking out a stack of books from the library is as simple as searching the library’s catalog and using unique call numbers to pull each book from their shelf locations. Using a similar principle, scientists at the Center for Functional Nanomaterials (CFN)—a U.S. Department of Energy (DOE) Office of Science User Facility at Brookhaven National Laboratory—are teaming with Harvard University and the Massachusetts Institute of Technology (MIT) to create a first-of-its-kind automated system to catalog atomically thin two-dimensional (2-D) materials and stack them into layered structures. Called the Quantum Material Press, or QPress, this system will accelerate the discovery of next-generation materials for the emerging field of quantum information science (QIS).
Structures obtained by stacking single atomic layers (“flakes”) peeled from different parent bulk crystals are of interest because of the exotic electronic, magnetic, and optical properties that emerge at such small (quantum) size scales. However, flake exfoliation is currently a manual process that yields a variety of flake sizes, shapes, orientations, and number of layers. Scientists use optical microscopes at high magnification to manually hunt through thousands of flakes to find the desired ones, and this search can sometimes take days or even a week, and is prone to human error.
Once high-quality 2-D flakes from different crystals have been located and their properties characterized, they can be assembled in the desired order to create the layered structures. Stacking is very time-intensive, often taking longer than a month to assemble a single layered structure. To determine whether the generated structures are optimal for QIS applications—ranging from computing and encryption to sensing and communications—scientists then need to characterize the structures’ properties.