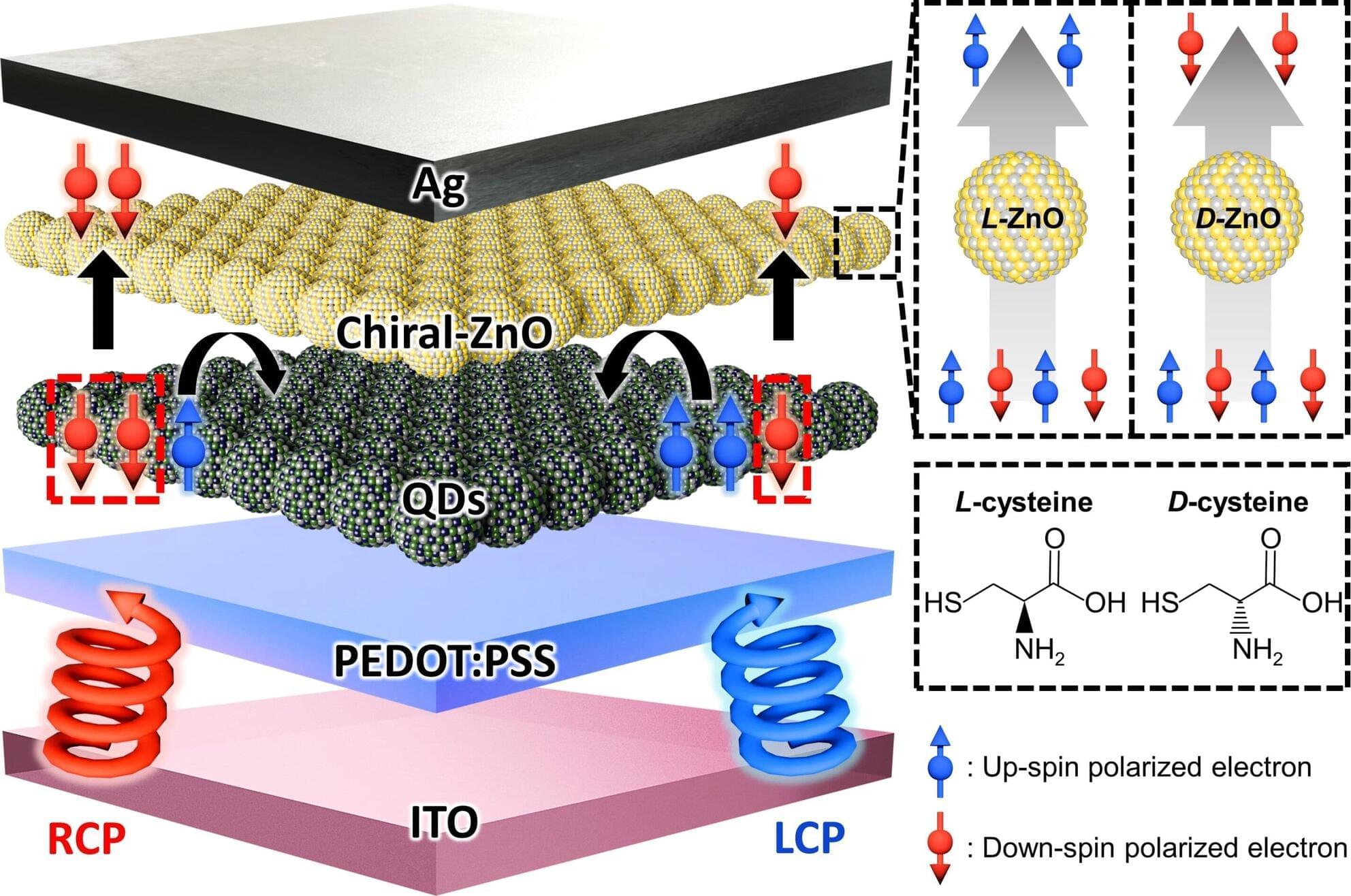
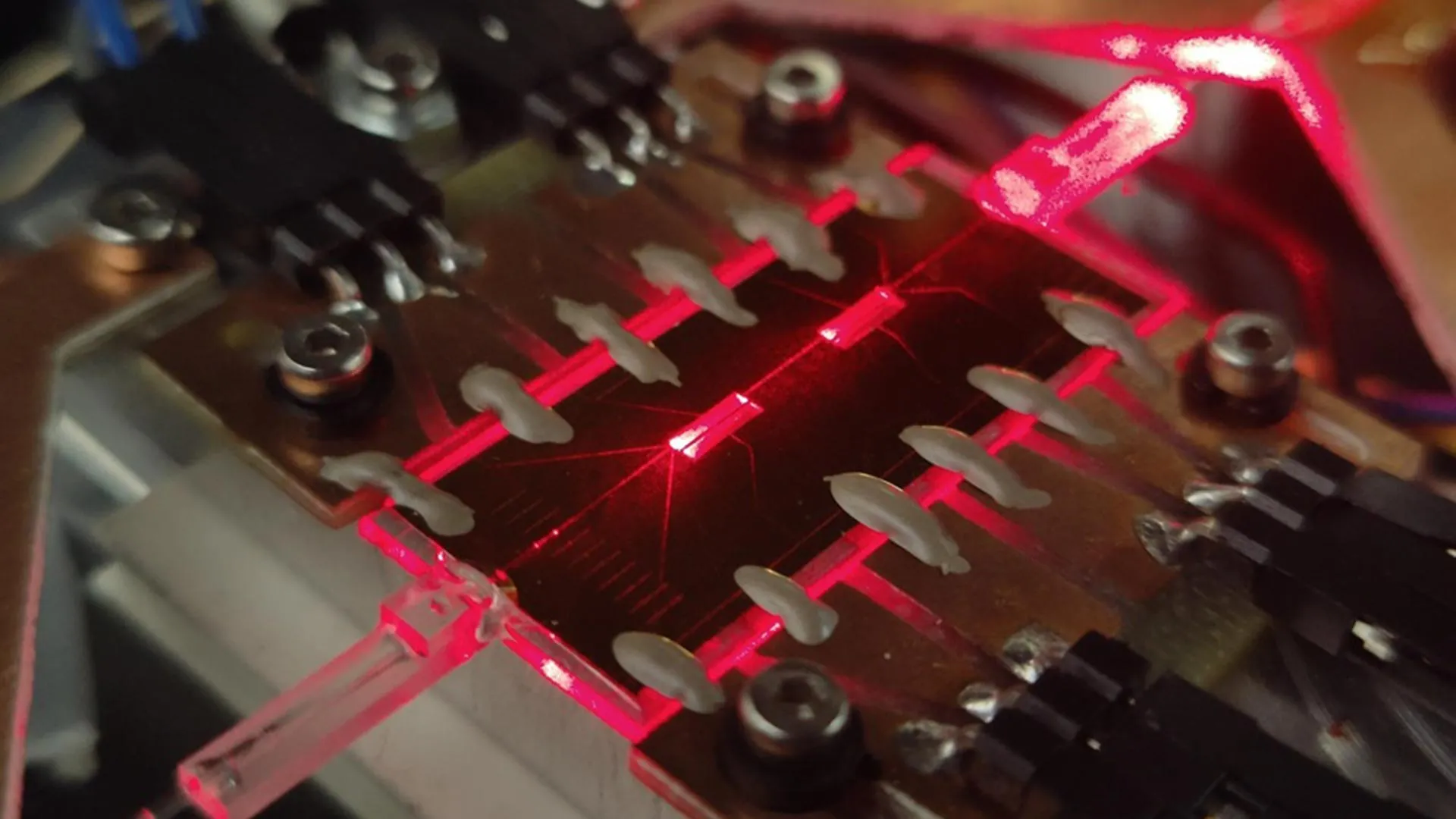
A research team led by Professor Jiwoong Yang of the Department of Energy Science and Engineering at DGIST has developed next-generation optical sensor technology capable of precisely detecting not only the intensity and wavelength of light but also its rotational direction—the spin information of photons. The team successfully implemented a quantum-dot-based optical sensor that can detect circularly polarized light (CPL) across an ultra-wide spectral range—from ultraviolet to short-wave infrared—demonstrating photodetection performance comparable to that of commercial silicon optical sensors. The paper is published in Advanced Materials.
CPL refers to light in which the electric field rotates helically as it propagates. This is directly linked to the spin information of photons—the fundamental particles of light. This polarization information serves as a crucial signal in next-generation security and communication technologies, such as quantum communication, quantum cryptography, and photonic quantum information processing, which is why related optical sensor technologies are attracting significant worldwide attention.
Conventional circularly polarized light sensors typically require the light-absorbing material itself to possess a specific helical orientation, known as a chiral structure. This approach not only limits the range of usable materials but also confines detection to narrow spectral regions, such as ultraviolet or visible light. Extending this technology into the infrared region, which is essential for quantum communication and optical sensing, has previously posed a major technical challenge.