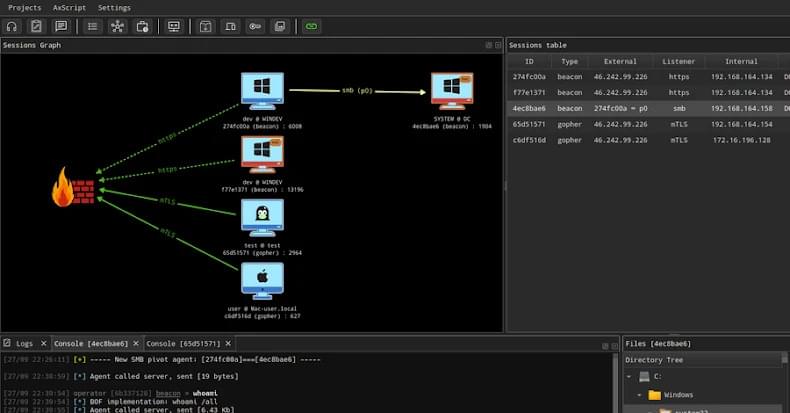
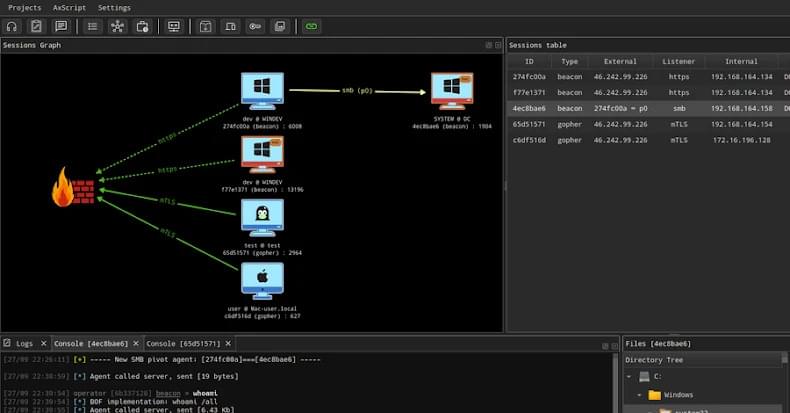
Open-source AdaptixC2, once for ethical hacking, is now used by Russian ransomware groups.

WhatsApp is rolling out passkey-encrypted backups for iOS and Android devices, enabling users to encrypt their chat history using their fingerprint, face, or a screen lock code.
Passkeys are a passwordless authentication method that allows users to sign in using biometrics (such as face recognition or fingerprint), PINs, or security patterns instead of traditional passwords. They enable logging into websites, online services, or apps without needing to remember complex passwords or use a password manager.
When creating a passkey, your device generates a unique cryptographic key pair consisting of a private key stored on the device and a public key sent to the website or app. Because of this, passkeys provide significantly improved security over regular credentials, seeing that they can’t be stolen in data breaches because the private key never leaves your device.

Near-Field Communication (NFC) relay malware has grown massively popular in Eastern Europe, with researchers discovering over 760 malicious Android apps using the technique to steal people’s payment card information in the past few months.
Contrary to the traditional banking trojans that use overlays to steal banking credentials or remote access tools to perform fraudulent transactions, NFC malware abuses Android’s Host Card Emulation (HCE) to emulate or steal contactless credit card and payment data.
They capture EMV fields, respond to APDU commands from a POS terminal with attacker-controlled replies, or forward terminal requests to a remote server, which crafts the proper APDU responses to enable payments at the terminal without the physical cardholder present.

Aardvark represents a breakthrough in AI and security research: an autonomous agent that can help developers and security teams discover and fix security vulnerabilities at scale. Aardvark is now available in private beta to validate and refine its capabilities in the field.
Aardvark continuously analyzes source code repositories to identify vulnerabilities, assess exploitability, prioritize severity, and propose targeted patches.
Aardvark works by monitoring commits and changes to codebases, identifying vulnerabilities, how they might be exploited, and proposing fixes. Aardvark does not rely on traditional program analysis techniques like fuzzing or software composition analysis. Instead, it uses LLM-powered reasoning and tool-use to understand code behavior and identify vulnerabilities. Aardvark looks for bugs as a human security researcher might: by reading code, analyzing it, writing and running tests, using tools, and more.




