After an early flurry of exploit activity, attacks targeting a maximum-severity flaw that Progress Software disclosed in its WS_FTP Server file transfer product last week appear to have been somewhat limited so far.
However, that’s no reason for organizations to delay patching the vulnerability as soon as possible, given how widely attackers exploited a similarly critical zero-day flaw that Progress reported in its MOVEit file transfer software in May.
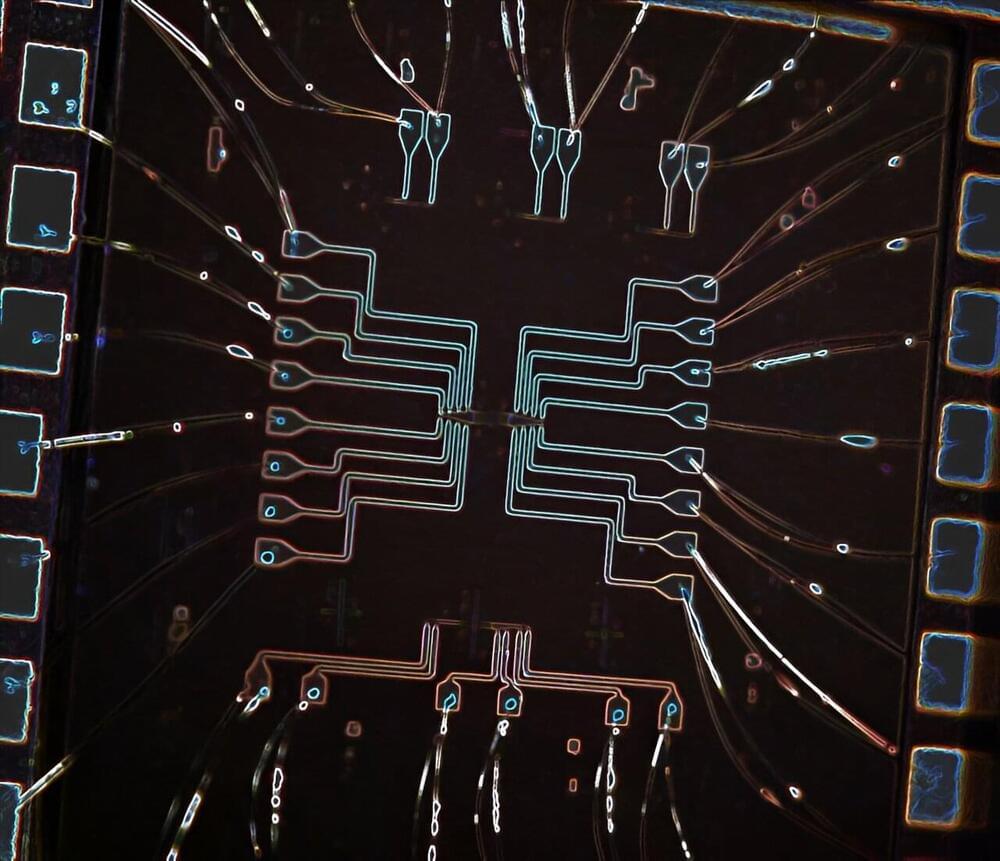
CVE-2023–40044 is a. NET deserialization vulnerability in WS_FTP that researchers have shown can be exploited with a single HTTPS POST and some specific multi-part data. Progress disclosed the bug on Sept. 27, with a recommendation for organizations to apply the company’s update for it as soon as possible.






 עברית (Hebrew)
עברית (Hebrew)