Europe’s largest parking app operator, EasyPark Group, faces a major data breach, urging heightened cybersecurity awareness.


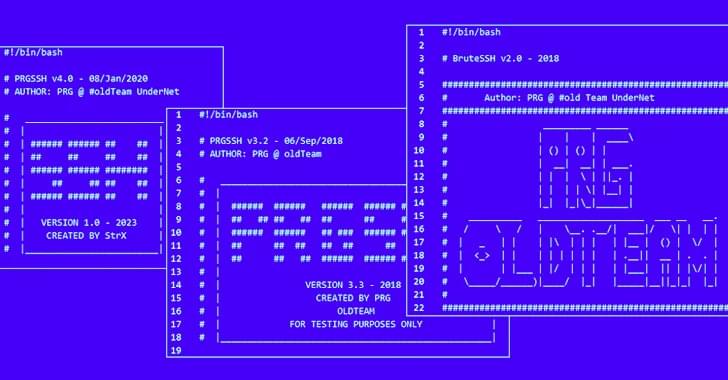
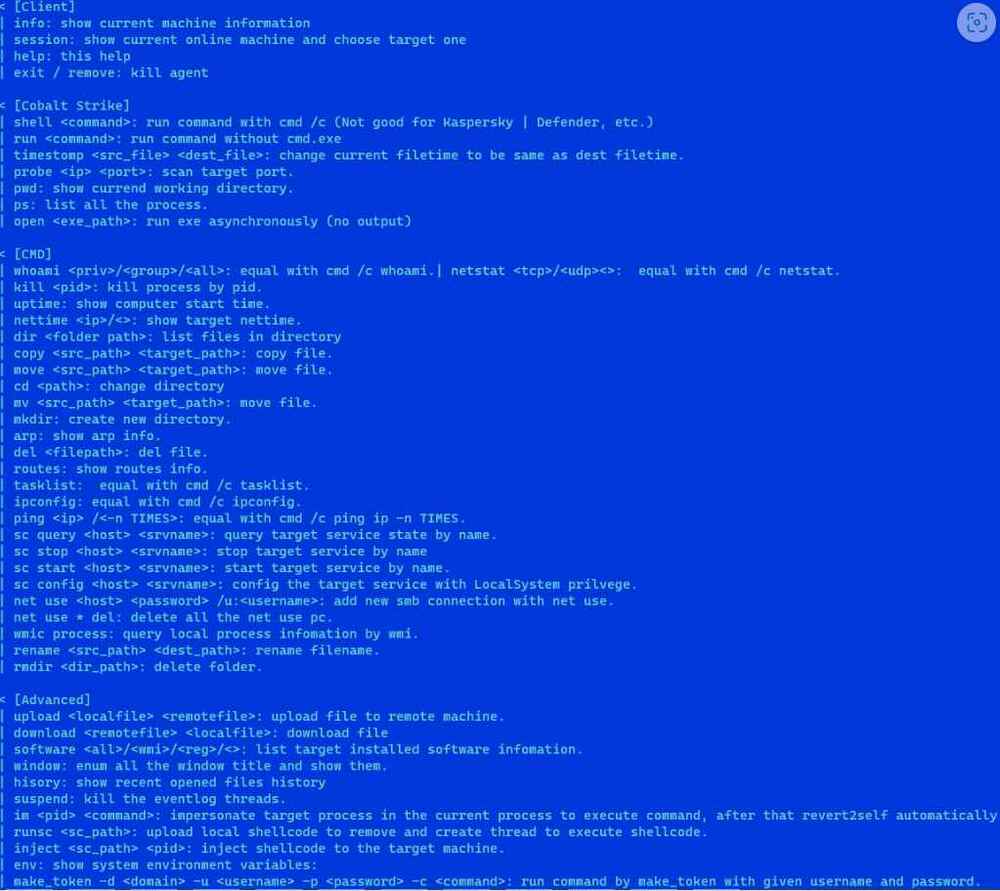
Poorly secured Linux SSH servers are being targeted by bad actors to install port scanners and dictionary attack tools with the goal of targeting other vulnerable servers and co-opting them into a network to carry out cryptocurrency mining and distributed denial-of-service (DDoS) attacks.
“Threat actors can also choose to install only scanners and sell the breached IP and account credentials on the dark web,” the AhnLab Security Emergency Response Center (ASEC) said in a report on Tuesday.
In these attacks, adversaries try to guess a server’s SSH credentials by running through a list of commonly used combinations of usernames and passwords, a technique called dictionary attack.

Google and Twitter ads are promoting sites containing a cryptocurrency drainer named ‘MS Drainer’ that has already stolen $59 million from 63,210 victims over the past nine months.
According to blockchain threat analysts at ScamSniffer, they discovered over ten thousand phishing websites using the drainer from March 2023 to today, with spikes in the activity observed in May, June, and November.
A drainer is a malicious smart contract or, in this case, a complete phishing suite designed to drain funds from a user’s cryptocurrency wallet without their consent.

Ubisoft reportedly stopped hackers from stealing 900GB of data from the company, including user data from the game Rainbow Six Siege.
The company reportedly discovered the breach 48 hours after the hack, at which point it revoked the hackers’ access before they could remove any data, BleepingComputer reports.
Still, the hackers reportedly were able to access Microsoft Teams conversations, the Ubisoft SharePoint server, and the Confluence and Mongo DB Atlas.




The threat actors associated with the 8220 Gang have been observed exploiting a high-severity flaw in Oracle WebLogic Server to propagate their malware.
The security shortcoming is CVE-2020–14883 (CVSS score: 7.2), a remote code execution bug that could be exploited by authenticated attackers to take over susceptible servers.
“This vulnerability allows remote authenticated attackers to execute code using a gadget chain and is commonly chained with CVE-2020–14882 (an authentication bypass vulnerability also affecting Oracle Weblogic Server) or the use of leaked, stolen, or weak credentials,” Imperva said in a report published last week.
