Cybersecurity researchers have detailed a “simple but efficient” persistence mechanism adopted by a relatively nascent malware loader called Colibri, which has been observed deploying a Windows information stealer known as Vidar as part of a new campaign.
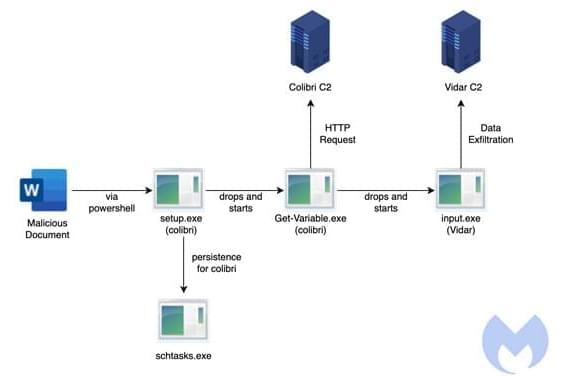
“The attack starts with a malicious Word document deploying a Colibri bot that then delivers the Vidar Stealer,” Malwarebytes Labs said in an analysis. “The document contacts a remote server at (securetunnel[.]co) to load a remote template named ‘trkal0.dot’ that contacts a malicious macro,” the researchers added.
First documented by FR3D.HK and Indian cybersecurity company CloudSEK earlier this year, Colibri is a malware-as-a-service (MaaS) platform that’s engineered to drop additional payloads onto compromised systems. Early signs of the loader appeared on Russian underground forums in August 2021.